Your cart is currently empty!
VIAVI Solutions

Threat Exposure Management
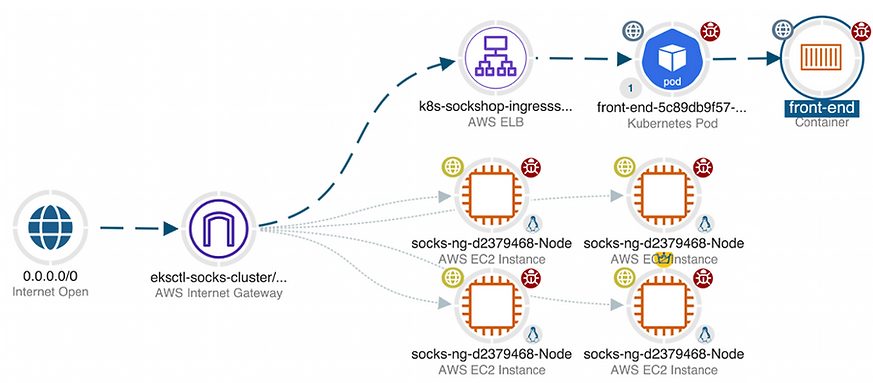
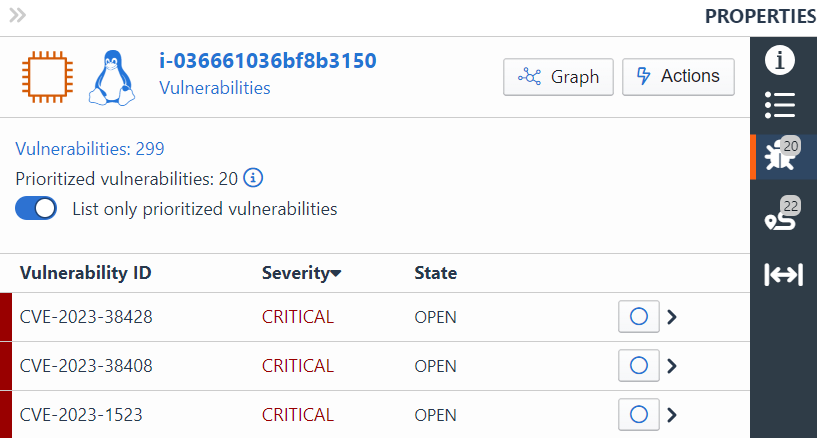
The VIAVI Threat Exposure Management solution analyzes and visualizes your AWS environment to help you pinpoint which cloud resources are most vulnerable to attack and confirms if and, when exposed assets have been compromised, providing a clear picture of your security posture.

Understanding the Cloud Security Landscape: Common Challenges
Threat Exposure Management addresses many of the common security pain points customers encounter as they strive to keep up with ever-changing cloud environments and service architectures.
Visibility Gaps
Ongoing human, system, and design changes make a passive approach to visibility unsustainable. Locking down systems reactively is not an acceptable approach for managing the interactions and permissive settings that may be creating new attack vectors.
Siloed Views
The elimination of siloed views is one key to optimizing visibility. With customers maintaining multiple AWS accounts and VPCs, each with potentially large numbers of resources, monitoring these assets individually is neither efficient nor adequate.
Automated Changes
Automation and continuous expansion and improvements have heightened the pace of change in the end-to-end AWS environment to one that many teams struggle to keep up with.
Data Volume
Critical insights pointing to compromise can be obscured by the sheer volume of data, potentially leading to extensive delays in detecting and mitigating issues. The rate and complexity of data flows also makes it challenging to understand the impact of a breach without the benefit of intelligent analysis and Continuous Threat Exposure Management (CTEM).
Observer Sentry: The Heart of VIAVI CTEM
Observer Sentry stands at the forefront of our Continuous Threat Exposure Management solution, offering a unique ability to continually visualize, analyze, and prioritize cloud security threats
CTEM Discovery
- Identifying less visible assets, vulnerabilities, and misconfigurations that were not considered during the initial scoping.
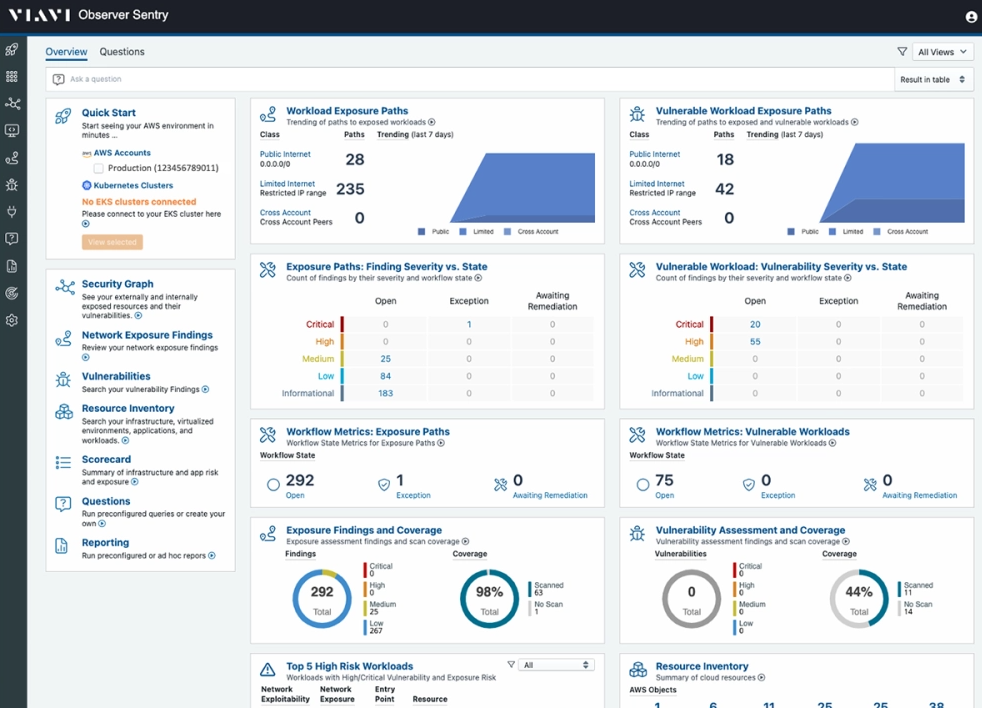
Threat Prioritization
- Identifying less visible assets, vulnerabilities, and misconfigurations that were not considered during the initial scoping.
Validating Attack Pathways
- Simulating attacks under real-world conditions to assess how the system reacts.